Configure Okta Mobile settings
The Okta Mobile app will transition to End of Life (EOL) status on May 31, 2026.
After this deprecation date, Okta Mobile will not receive any further security updates, bug fixes, or support. The app will no longer be available for download through the Apple App Store or the Google Play Store.
Okta previously announced the End of Support for Okta Mobile, effective November 1, 2025.
See Okta Mobile End of Life for available migration solutions.
As an administrator, you can configure Okta Mobile settings to define how end users access Okta Mobile and their apps on devices.
Before you begin
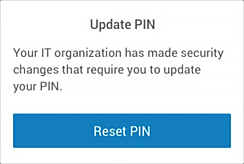
Changes to Okta Mobile security settings may take up to 24 hours to be applied to all the eligible end users in your org and for Okta to prompt those end users to update their PIN.
Start this task
- In the Okta Admin Console, go to .
- Click Edit to configure the Okta Mobile settings.
- Save your settings.
|
PIN length |
Specify the required number of digits for the PIN. |
|
Allow simple PIN |
Select the check box to permit the use of repeating, ascending, and descending numeric sequences (such as 1111, 1234, 4321, etc.). |
|
Ask for PIN when user is inactive for |
Specify how long users can be inactive before they are prompted to enter a PIN. Users must re-authenticate after prolonged Okta Mobile inactivity. Users who haven't used Okta Mobile for 30 days or longer, are prompted to enter their Okta credentials when they eventually open Okta Mobile. This occurs because Okta Mobile relies on an internal token for authentication that expires after 30 days of inactivity. This token expiration is different than PIN and MFA expiration occurrences. |
|
PIN expires after |
Specify how long the PIN is valid before it expires. |
|
Device trust |
Select the check box to apply existing device trust app sign-in policies to apps that end users access through Okta Mobile. This setting is enabled by default. If you haven't configured device trust policies to apps, or if device trust is not enabled for your org (), selecting this setting has no effect. |
|
Screen preview/capture (Android only) |
When this option is selected, Android device users can't take screenshots, record videos, or share their screen from within Okta Mobile. Other apps are not affected. Requires Okta Mobile 3.8.0 or later versions. For iOS device users, this option has no effect. |
|
Sign on to SAML apps (iOS only) |
This iOS-specific option allows users to access SAML apps in iOS Safari by using an extension. |
Related topics