CASB configuration guide
A cloud access security broker (CASB) is a software tool or service that sits between an organization's on-premises infrastructure and a cloud provider's infrastructure. A CASB acts as a gatekeeper, allowing the organization to extend the reach of their security policies beyond their own infrastructure.
CASB and the Okta OIN
To simplify integrating with inline or reverse proxy CASBs, Okta has developed functionality that allows admins to override various default settings associated with Okta's published OIN apps that use SAML for federation. The settings can also be applied to the Microsoft Office 365 app.
The values that can be overridden are:
- Assertion Consumer Service URL (ACS)
- Audience
- Destination
- Recipient
To override these settings admins must use the Okta API to populate the $app.settings.signOn object with the appropriate override values, as shown here:
| SAML Property | SignOn | Example Value |
|---|---|---|
| Assertion Consumer Service URL |
ssoAcsUrlOverride
|
https://casb-provider.com/ssoAcsUrlOverride
|
| Audience |
audienceOverride
|
https://casb-provider.com/audienceOverride
|
| Destination |
destinationOverride
|
https://casb-provider.com/destinationOverride
|
| Recipient |
recipientOverride
|
https://casb-provider.com/recipientOverride
|
Configure CASB for a Specific App
Here's an example of how to configure CASB for a specific app:
You can use an iframe to embed an end-user home page into your existing portal.
-
In the Admin Console, go to .
-
Create an API token.
-
Get the app details by making an API call as follows:
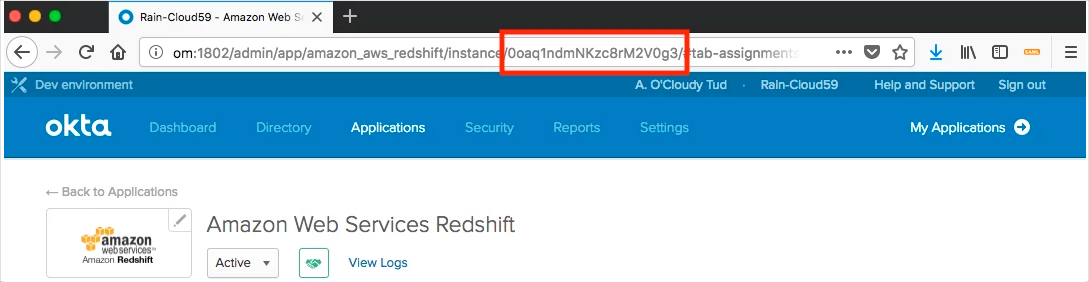
curl -X GET \ https://{{Okta host}}/api/v1/apps/{{App ID}} \ -H 'Authorization: SSWS {{ API Key }}' \ -H 'Accept: application/json'The API ID can be obtained from your app's URL, as shown here:
-
Copy the API response into a text editor.
-
Update the app data with an API call as shown in the following example.
Note:The attributes displayed are the minimum required ones. Replace the actual values with your saved data (see the
signOnsection in your API response).curl -X PUT \ https://{{Okta host}}/api/v1/apps/{{App ID}} \ -H 'Authorization: SSWS {{ API Key }}' \ -H 'Accept: application/json' \ -H 'Content-Type: application/json' \ -d '{ "label": "Amazon Web Services", "name": "amazon_aws", "signOnMode": "SAML_2_0", "settings": { "app": { "appFilter": null, "awsEnvironmentType": "aws.amazon", "groupFilter": "aws_(?{{accountid}}\\d+)_(?{{role}}[a-zA-Z0-9+=,.@\\-_]+)", "secretKey": null, "accessKey": null, "loginURL": "https://console.aws.amazon.com/ec2/home", "identityProviderArn": "arn:aws:iam::456272127071:saml-provider/OktaRainVladDobrikov2,arn:aws:iam::456272127071:role/RoleOktaRainVladDobrikov", "overrideAcsURL": null, "sessionDuration": 3600, "secretKeyEnc": null, "roleValuePattern": "arn:aws:iam::${accountid}:saml-provider/OKTA,arn:aws:iam::${accountid}:role/${role}" }, "signOn": { "defaultRelayState": "defaultRelayStateOverride", "ssoAcsUrlOverride": "https://casb-provider.com/ssoAcsUrlOverride", "audienceOverride": "https://casb-provider.com/audienceOverride", "recipientOverride": "https://casb-provider.com/recipientOverride", "destinationOverride": "https://casb-provider.com/destinationOverride" } } }'For Office 365, ensure that WS-Federation Configuration is set to Manual. Automatic configurations with multiple domain federation cause an error.
-
Perform a SAML sign-in from Okta for the application you updated.