Add SharePoint (On-Premises) in Okta
Follow these steps to add the SharePoint (On-Premises) app integration to your Okta org.
Before you begin
-
Install a supported version of Microsoft SharePoint:
- SharePoint Foundation 2013
- SharePoint Server 2013
- SharePoint Server 2016
- SharePoint Server 2019
- Run the prerequisites from the SharePoint installer.
- Fulfill hardware requirements.
-
Fulfill version-specific requirements:
Version Requirements SharePoint People Picker (versions before 2.3.0.0) Install .NET Framework 3.5+ SharePoint People Picker version 2.3.0.0 Ensure your server supports TLS 1.2 SharePoint 2013, 2016, or 2019 Install either of the following:
-
.NET Framework 4.5+, which supports TLS 1.2
-
.NET Framework 3.5+ and one of the patches provided here
-
-
A valid API token for the Okta People Picker plugin to read users and groups from Okta. See API.
CAUTION:The API token is only visible upon creation and can't be retrieved later. If the token is lost, it must be revoked, regenerated, and reconfigured in the People Picker configuration.
Start this procedure
-
In the Admin Console, go to .
-
Click Browse App Catalog.
-
Search for and select
SharePoint (On-Premises). Click Add Integration. -
In the General Settings tab, enter the values for your instance. These values are used to connect and send information as part of the SAML assertion to SharePoint.
-
SharePoint Web Application URL: This points to the web app that is running on SharePoint. For example,
https://app1. There can be multiple apps running on SharePoint, each of which needs a SharePoint app within Okta. -
Application attributes: Admins can send information about Okta user profile attributes to SharePoint for auditing or logging purposes. Sending any custom Okta attributes is also supported. This information isn't used for authentication or authorizing apps in SharePoint. Okta typically sends UPN and email data as part of the assertion.
App attributes can be in any of these formats:
-
Okta User Profile Attribute: For example,
firstName|${user.firstName}|http://okta.com/claims -
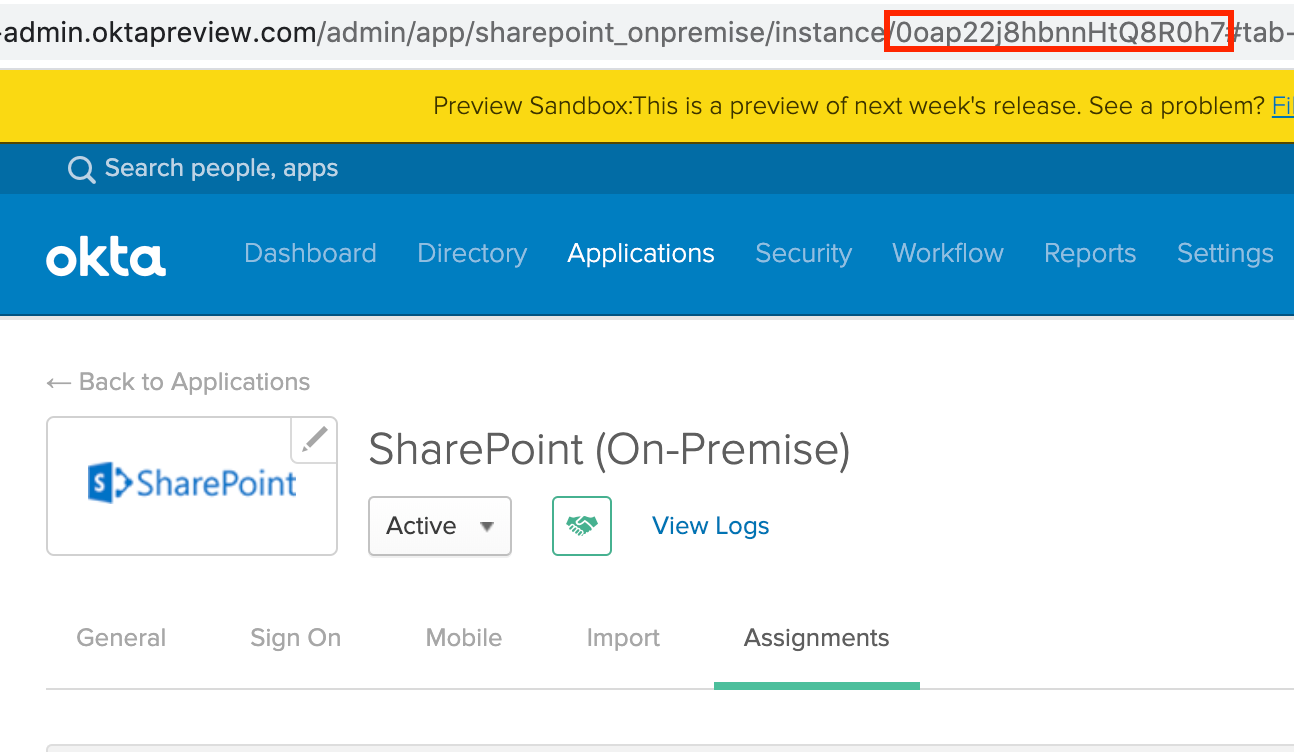
Imported Attribute: For example,
lastName|<appId>:${user.lastName}|http://okta.com/claimsYou can obtain your app ID from your app's URL as follows:
-
Okta User Profile Attribute: For example,
- Group filter: This field is sent as part of a SAML assertion. This is used for checking permissions in SharePoint.
-
SharePoint Web Application URL: This points to the web app that is running on SharePoint. For example,
-
Go to to install and configure SharePoint People Picker 2.3.0.0.
Okta Group Push isn't supported with the SharePoint (On-Premises) app.
Okta recommends that you use only AD groups or only Okta groups to configure authorization to your SharePoint server. Configuring Push Groups to your Active Directory and attempting to use these groups for SharePoint authorization results in problems accessing the app.
Next steps
Configure Okta as Claims Provider in SharePoint (On-Premises)