Configure Okta Verify
Configure how users authenticate with Okta Verify. Use MFA enrollment policies to enable Okta Verify at the org or group level.
Okta Verify is supported on several operating systems. See Supported platforms for Okta Verify .
-
In the Admin Console, go to .
- On the Factor Types tab, select Okta Verify .
- Set the status to Active.
- In
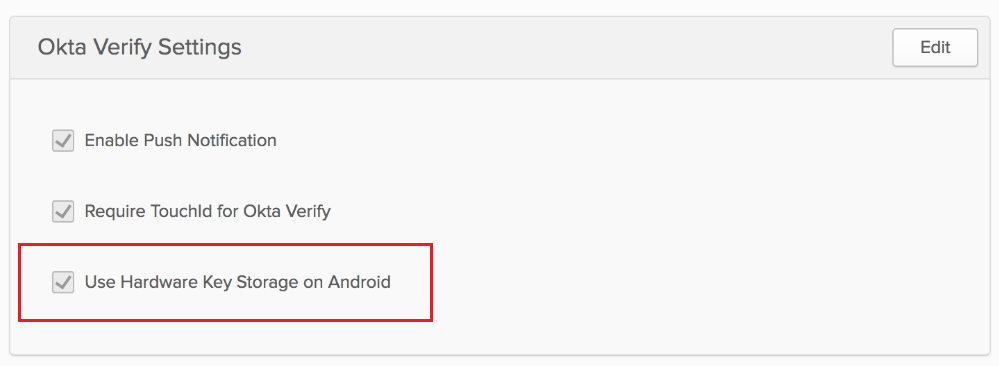
Okta Verify Settings, click Edit. Settings might vary by org.
- Enable Push Notification: Okta sends a prompt to the Okta Verify app on the user's mobile device. The user taps the prompt to verify their identity. This feature is available on Android and iOS mobile devices. It's not available on iPod Touch devices. See About Push Notification and end users.
- : iOS device users authenticate with Touch ID or Face ID. See About Apple TouchID and FaceID.
- Enable FIPS-Mode Encryption: Apply FIPS-mode encryption to enhance the protection of Okta Verify data. See About FIPS-mode encryption.
- Number Challenge: This option prevents users from accepting fraudulent push notifications. Configure when Okta Verify presents a number challenge: Never, Only for high risk sign-in attempts, or for All push challenges.
-
Use hardware key storage for Android devices:
This is an Early Access feature. To enable it, please contact Okta Support.
To enhance security on Android devices, enable this setting. It allows you to implement the Federal Identity, Credential, and Access Management (FICAM) security architecture. This setting applies access control and hardware protection to keys stored on Android devices.
- Click Save.
User experience
Push Notification
After you enable Okta Verify with Push Notification, users are prompted to enable this option the next time they sign in to Okta. The Okta Verify app guides them through the setup. See Okta Verify (Documentation for end users).
Okta Verify user enrollments are associated with your Okta subdomain. If you rename your Okta subdomain, reset all of your active Okta Verify enrollments. See Rename your Okta subdomain.
Push notification and number challenge
Ensure that you meet these prerequisites:
- Your org uses a customized Sign-In Widget with a version number of 3.3.0 or later.
- If your org calls the Authentication API directly, update your code to handle the number challenge API response. See Response example (waiting for 3-number verification challenge response).
If you enabled Push Notification with Number Challenge, users validate their sign-in attempt by completing a number matching challenged in addition to approving a push notification in Okta Verify. On their mobile devices, users approve the push notification and tap the numbers that appear in the Sign-In Widget. Users are granted access only if they tap the correct number. If the user taps No, It's Not Me, the sign-in attempt is blocked.
This feature isn't supported in LDAPi and RADIUS environments. Okta Verify skips the number matching challenge. For these environments, configure a different MFA factor and not Okta Verify.
Set the push notifications to Optional to allow multiple enrollments to use the Okta Verify number challenge.
Number challenge and risk scoring
You can combine the number challenge functionality with risk scoring to enhance the level of security for your Okta org and guard against malicious sign-in attempts.
When Risk Scoring is enabled, Okta assesses risk based on criteria such as device details and location. It assigns a risk level to each Okta sign-in attempt. You can configure a sign-on policy rule to respond in different ways based on risk level. For example, Okta can prompt users for multifactor authentication if the sign-in attempt is considered high risk. See Risk scoring for instructions.
Use Okta Verify with Push and RADIUS agents
To use Okta Verify Push and the Okta RADIUS agent, your agent version must be 2.1.5 or later. See Okta RADIUS Server Agent Version History.
Apple Touch ID and Face ID
Apple Touch ID and Face ID use biometric technology to guard against unauthorized use of Okta Verify. You can configure a user fingerprint or facial recognition request, which appears after the initial MFA challenge. If the user's device is lost or stolen, no one else can gain access to it. This feature is only available for iOS devices.
When Touch ID and Face ID are enabled, users are prompted to configure Touch ID or Face ID for their device when they enroll or authenticate. Okta Verify guides users through this configuration.
If users are already enrolled in Okta Verify Push and you enable Touch ID and Face ID, users are prompted for biometrics the next time they authenticate with Okta Verify Push:
- If Touch ID and Face ID aren't yet enabled on the device, users are prompted with Touch ID Required or Face ID Required.
- If Touch ID and Face ID are enabled on the device, users are prompted with Touch ID for Okta Verify or Face ID for Okta Verify .
About FIPS-mode encryption
The Federal Information Processing Standards (FIPS) is a set of technical requirements developed by the United States government to establish computer security guidelines for government agencies, corporations, and organizations.
When FIPS-mode encryption is enabled, Okta Verify uses FIPS 140-2 validation for all security operations to ensure secure interoperability.
Okta also meets FedRAMP FICAM requirements by relying on FIPS-validated vendors.
See Supported platforms for Okta Verify .
When you enable this option, Android devices are FICAM-compliant only if users configure and set a secure PIN on their devices.
Related topics