Step 1: Configure Workspace ONE Access as an Identity Provider in Okta
This is an Early Access feature. To enable it, in the Okta Admin Console, go to , and then turn on Workspace1 Device Trust for your mobile platform(s).
This section describes how to configure Workspace ONE Access as an identity provider (IdP) in Okta. This configuration is required to configure a unified catalog as well as mobile SSO and device trust.
For additional information, see Typical workflow for configuring inbound SAML.
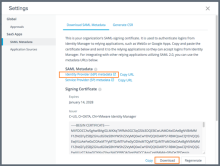
Get Workspace ONE Access SAML Metadata Information
Retrieve the SAML metadata information from Workspace ONE Access that is required to set up an identity provider in Okta.
- Log in to the Workspace ONE Access console as the System administrator.
- Select the tab.
- Click Settings.
- Click SAML Metadata in the left pane.
The Download Metadata tab is displayed.
- Download the Signing Certificate.
- In the Signing Certificate section, click Download.
- Make a note of where the certificate files is downloaded (signingCertificate.cer).
- Retrieve the SAML metadata.
- In the SAML Metadata section, right-click the Identity Provider (IdP) metadata link and open it in a new tab or window.
- In the identity provider metadata file, find and make a note of the following values:
- entityID
For example: https://tenant.vmwareidentity.com/SAAS/API/1.0/GET/metadata/idp.xml
- SingleSignOnService URL with Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-POST"
For example: https://tenant.vmwareidentity.com/SAAS/auth/federation/sso
- entityID
Add an Identity Provider in Okta
For additional information about how Okta handles external identity providers, see Identity Providers.
- In the Okta Admin Console, go to .
- Click Add Identity Provider and select SAML 2.0 IdP.
- Click Next.
- Enter a name for the identity provider. For example, Workspace ONE.
- Configure the following:
- IdP Username: Enter idpuser.subjectNameId.
If you plan to send the username in a custom SAML attribute, define an appropriate expression. For information, see Okta Expression Language.
- Filter: Do not select this checkbox.
- Match against: Select Okta Username.
Adjust the selection as required for your environment and the values that you plan to send.
- If no match is found: Select Redirect to Okta sign-in page.
- IdP Issuer URI: Enter the entityID.
This is the value you obtained from the identity provider metadata file from Workspace ONE. For example, https://tenant.vmwareidentity.com/SAAS/API/1.0/GET/metadata/idp.xml
- IdP Single Sign-On URL: Enter the SingleSignOnService Location URL.
This is the value you obtained from the identity provider metadata file from Workspace ONE. For example, https://tenant.vmwareidentity.com/SAAS/auth/federation/sso
- IdP Signature Certificate: Browse and select the Signing Certificate file you downloaded from Workspace ONE in Get Workspace ONE Access SAML Metadata Information.
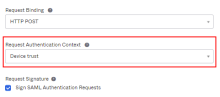
- Request Authentication Context: Select Device Trust.
This setting specifies the context of the authentication request.
If the Request Authentication Context option is not available, go to and enable Workspace1 Device Trust for your mobile platform(s).
- IdP Username: Enter idpuser.subjectNameId.
- Click Finish.
- Verify that the following information appears:
- SAML Metadata
- Assertion Consumer Service URL
- Audience URI
-
Download and save the metadata file.
Click the Download Metadata link.
Save the metadata file locally.
Open the metadata file and copy its contents for use in Get Workspace ONE Access SAML Metadata Information.