RADIUS applications in Okta
Okta can distinguish between different RADIUS-enabled apps and support them concurrently by setting up an Okta RADIUS app for each configuration. Additionally, the Okta RADIUS application supports policy creation and assignment of the application to groups.
RADIUS-enabled apps are easy to manage, as Admins can manage all of these apps and infrastructure configurations from the Okta Admin Console.
Limitations
Enroll only a single Okta Verify device. Adding more Okta Verify devices can cause undefined or unexpected behavior.
If you've migrated a RADIUS-configured org from Classic Engine and you configure the Okta Verify authenticator with the number challenge, the challenge may be presented to RADIUS users even though it's not supported. To prevent this, enable the Early Access feature Disable number matching challenge for RADIUS. See Manage Early Access and Beta features.
Supported factors
The size of the challenge message can be too large for the RADIUS prompt if you let users enroll too many authenticators. Okta recommends that you enroll no more than eight authenticators at a given time.
Okta supports the following authenticators for RADIUS apps:
|
MFA Authenticator |
Password Authentication Protocol (PAP) | Extensible Authentication Protocol - Generic Token Card (EAP-GTC) | Extensible Authentication Protocol - Tunneled Transport Layer Security (EAP-TTLS)* |
|---|---|---|---|
| Duo (Push, SMS, and Passcode only) | Supported | Supported | Duo passcode only. |
|
Supported |
Supported |
Supported when the string "EMAIL" is initially sent. Refer to associated note. |
|
|
RADIUS doesn't support inline enrollment with Email. When using inline enrollment, either disable Email or specify Password reset in Email settings. 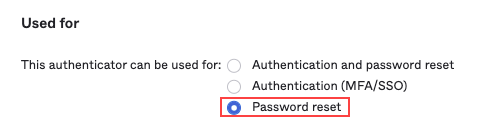
|
|||
| Supported | Supported | Supported, as long as challenge is avoided. For example MFA only or "Password, passcode". | |
| Supported (for one device only) |
Supported (for one device only) |
Supported as long as challenge is avoided. (for one device only) For example: MFA-only or "Password, MFA" for TOTP. Push can work with primary authentication with MFA as the push challenge is sent out-of-band. |
|
|
Not supported |
Not supported |
Not supported |
|
| Supported (Password and MFA only) | Supported (Password + MFA only). | Not supported | |
| Supported | Supported | Supported when the string "CALL" is sent. Refer to associated note. | |
| Supported | Supported | Supported - as long as challenge is avoided. For example MFA only or "Password, passcode". | |
* RADIUS supports three authentication methods:
- Password + MFA: Primary authentication using password, then the user is prompted to select factors to complete the authentication.
- MFA Only: Instead of password, users enter either a one-time passcode (OTP), or one of
EMAIL,SMS,CALL,PUSH(case insensitive). - Password and Passcode: Password entered immediately followed by a passcode in a request. Must be in the same request, for example:
Abcd1234,879890" or "Abcd1234,SmS".
Protocols support the following authentication methods:
| Protocol | Supports |
|---|---|
| PAP | Password and MFA, MFA, "Password and passcode". |
| EAP-TTLS | MFA only, "Password and passcode". |
| EAP-GTC | Password and MFA, MFA only, "Password and passcode". |
Users must send the specified string EMAIL/SMS/CALL, which initially returns a failure. This results in the generation of an OTP provided using the specified method. The provided OTP can then be used for authentication.
EAP-TTLS doesn't support enrollment
Authentication will fail unexpectedly when EAP-TTLS is enabled, either Okta Verify or Phone are specified as the required enrollment policy, and the user isn't enrolled in that authenticator.
U2F Security and Windows Hello aren't compatible with RADIUS-enabled implementations. See RADIUS applications in Okta.
Passwordless authentication
RADIUS authentication uses passwords as the primary authentication mechanism. Traditional RADIUS authentication can't be performed with passwordless users. RADIUS can use other factors for authentication when the application setting property Okta performs primary authentication is cleared. See 2FA Only (Passwordless Mode) in RADIUS applications in Okta for addition detail.
For more information on passwordless authentication see Set up passwordless sign-in experience.
Supported features and limitations
Features
-
Support for multiple RADIUS-enabled apps and infrastructure
Each app and infrastructure component (for example, VPNs), can be uniquely configured using the same Okta RADIUS agent. The agent can listen to multiple distinct ports for separate RADIUS configurations. For example, while Cisco AnyConnect uses RADIUS UDP port 1812, another on-premises app can use RADIUS UDP port 1813.
-
User- and group-specific configurations
Admins can limit access to RADIUS-enabled apps and infrastructure to specific users and groups.
-
Pass group ownership to RADIUS applications
Okta passes a list of a user's groups to a RADIUS-enabled app or infrastructure. This allows admins to support fine-grained authorization with different levels of access and security based on group membership.
-
Provide multifactor authentication and security based on IP addresses
When they resolve the IP address of a client that attempts to connect to a RADIUS-enabled app or infrastructure, admins can set their access based on whether a user is within a certain IP range or network zone. See Network.
-
Centralized, cloud-based configuration
Administrators can manage all of their RADIUS-enabled apps and infrastructure configurations from the Okta Admin Console, without making changes on the Okta RADIUS Agent server itself.
-
2FA Only (Passwordless Mode)
You can configure a RADIUS-enabled app to only use the second factor in multifactor authentication. This is also known as passwordless mode.
When you configure the app to enable 2FA mode, clear the Okta performs primary authentication checkbox, ensure you use a unique UDP port, and verify the Application username format.
Limitations
- The RADIUS port and shared secret are captured from the Okta Admin Console through any configured RADIUS applications or VPNs. Any information entered from prompts from the RADIUS agent is available if an org enables the feature after the information is entered.
- WiFi infrastructure isn't supported.
- The RADIUS agent only supports PAP-based authentication. No other protocols are supported.
Typical workflow
|
Task |
Description |
|---|---|
| Download the RADIUS agent |
In the Admin Console, go to . Download the appropriate Okta RADIUS Agent for your environment. |
| Install Okta RADIUS Server agent on Windows | Install the Okta RADIUS Server agent for your platform. |
| Add the RADIUS application | Add the generic RADIUS application and create and configure a group. |
| Configure the RADIUS customer application | Configure the customer application. |
| Test | Validate and test the integration. |
| Client IP reporting | Optional. You can configure Okta to enforce, restrict, or provide different levels of access to users who access your RADIUS-enabled system, based on their IP address or network zone. |
| Okta group membership information for authorization | Optional. You can configure Okta to provide different levels of authorization and access to a RADIUS-enabled service users based on which groups users belong to. |
| RADIUS service address filtering | Optional. For additional security, you can choose to limit access to RADIUS services by entering an IP address for a specific network adapter, or by adding a list of IP addresses (for example, VPN servers). This ensures that RADIUS services aren't accessed by unauthorized hosts. |