Configure Cisco Firepower Management Center
Configure Cisco Firepower Management Center (FMC) to use the Okta RADIUS Server agent for multifactor authentication.
Okta provides the ability for organizations to manage authorization and access to on-premises applications and resources using the RADIUS protocol and the Okta RADIUS agent. With the Okta RADIUS Advanced Server Access server agent, organizations can delegate authentication to Okta.
Typical architecture
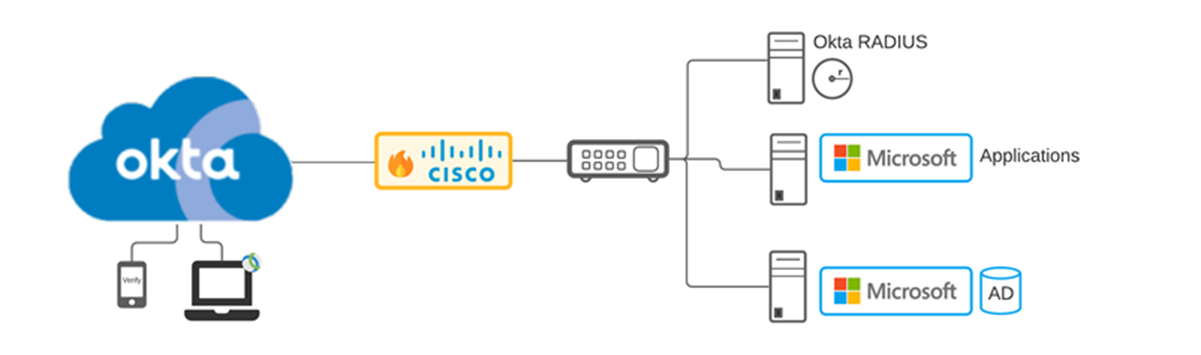
Clients often use the Cisco AnyConnect Secure Mobility client to connect to a Cisco Firepower firewall. Users are authenticated using the Okta RADIUS agent backed by Microsoft Active Directory. The authentication process uses MFA. See Supported authenticators.
Before you begin
Meet the following network connectivity requirements before you install the Okta RADIUS agent:
| Source | Destination | Port/Protocol | Description |
|---|---|---|---|
| Okta RADIUS Agent | Okta Identity Cloud | TCP/443 HTTP |
Configuration and authentication traffic. |
| Client Gateway | Okta RADIUS Agent | UDP/1812 RADIUS (Default, you can change this when you install and configure the RADIUS app) | RADIUS traffic between the gateway (client) and the RADIUS agent (server). |
Supported authenticators
The size of the challenge message can be too large for the RADIUS prompt if you let users enroll too many authenticators. Okta recommends that you enroll no more than eight authenticators at a given time.
Okta supports the following authenticators for RADIUS apps:
|
MFA Authenticator |
Password Authentication Protocol (PAP) | Extensible Authentication Protocol - Generic Token Card (EAP-GTC) | Extensible Authentication Protocol - Tunneled Transport Layer Security (EAP-TTLS)* |
|---|---|---|---|
| Duo (Push, SMS, and Passcode only) | Supported | Supported | Duo passcode only. |
|
Supported |
Supported |
Supported when the string "EMAIL" is initially sent. Refer to associated note. |
|
|
RADIUS doesn't support inline enrollment with Email. When using inline enrollment, either disable Email or specify Password reset in Email settings. 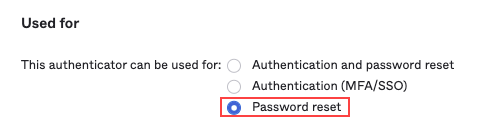
|
|||
| Supported | Supported | Supported, as long as challenge is avoided. For example MFA only or "Password, passcode". | |
| Supported (for one device only) |
Supported (for one device only) |
Supported as long as challenge is avoided. (for one device only) For example: MFA-only or "Password, MFA" for TOTP. Push can work with primary authentication with MFA as the push challenge is sent out-of-band. |
|
|
Not supported |
Not supported |
Not supported |
|
| Supported (Password and MFA only) | Supported (Password + MFA only). | Not supported | |
| Supported | Supported | Supported when the string "CALL" is sent. Refer to associated note. | |
| Supported | Supported | Supported - as long as challenge is avoided. For example MFA only or "Password, passcode". | |
* RADIUS supports three authentication methods:
- Password + MFA: Primary authentication using password, then the user is prompted to select factors to complete the authentication.
- MFA Only: Instead of password, users enter either a one-time passcode (OTP), or one of
EMAIL,SMS,CALL,PUSH(case insensitive). - Password and Passcode: Password entered immediately followed by a passcode in a request. Must be in the same request, for example:
Abcd1234,879890" or "Abcd1234,SmS".
Protocols support the following authentication methods:
| Protocol | Supports |
|---|---|
| PAP | Password and MFA, MFA, "Password and passcode". |
| EAP-TTLS | MFA only, "Password and passcode". |
| EAP-GTC | Password and MFA, MFA only, "Password and passcode". |
Users must send the specified string EMAIL/SMS/CALL, which initially returns a failure. This results in the generation of an OTP provided using the specified method. The provided OTP can then be used for authentication.
EAP-TTLS doesn't support enrollment
Authentication will fail unexpectedly when EAP-TTLS is enabled, either Okta Verify or Phone are specified as the required enrollment policy, and the user isn't enrolled in that authenticator.
U2F Security and Windows Hello aren't compatible with RADIUS-enabled implementations. See RADIUS applications in Okta.
Passwordless authentication
RADIUS authentication uses passwords as the primary authentication mechanism. Traditional RADIUS authentication can't be performed with passwordless users. RADIUS can use other factors for authentication when the application setting property Okta performs primary authentication is cleared. See 2FA Only (Passwordless Mode) in RADIUS applications in Okta for addition detail.
For more information on passwordless authentication see Set up passwordless sign-in experience.
Supported versions, clients, and features
Versions
| Software version | Role |
| Windows Server 2016 Standard | Windows domain controller |
| Windows Server 2016, 2019 Standard | Windows application server |
| Cisco Firepower Thread Defense 6.4.0.9 | NGFW Firewall |
| Cisco Firepower Virtual Management Center | NGFW Management |
The Okta RADIUS server agent has been tested on the following Linux versions:
- Red Hat Enterprise Linux release 8.0, 8.3, 9.0
- CentOS 7.6
- Ubuntu 18.04.4, 20.04.1 LTS
Clients
| Software version | Role |
|
Windows 10 |
Desktop client |
|
Cisco Anyconnect Secure Mobility Client 4.6.01103 |
Windows remote VPN agent |
Typical workflow with Active Directory integration
|
Task |
Description |
|---|---|
| Download the RADIUS agent |
In the Admin Console, go to . Download the appropriate Okta RADIUS Agent for your environment. |
|
Install the agent |
Install Okta RADIUS Server agent on Windows |
| Optional. Download, install, and configure the Okta Active Directory (AD) Agent |
In the Admin Console, go to . Download the Okta AD Agent Installer.Install and configure the Okta AD Agent. See Get started with Active Directory integration. Note:
The Active Directory user chosen for this process only needs domain user capabilities. Okta recommends that you install the agent with administrator privileges on a server that has Windows AD RSAT tools installed. |
| Configure RADIUS application in Okta |
Configure the Cisco Advanced Server Access - RADIUS app. Note:
This integration works with all RADIUS applications. |
| Configure Cisco Firewall Management Center | Configure firewall management for RADIUS. |
| Test the Cisco Firepower Management Center integration | Test the agent. |