Multifactor authentication
Multifactor authentication (MFA) means that users must verify their identity in two or more ways to gain access to their account. This makes it harder for unauthorized parties to sign in to a user's account. It's unlikely that they have access to all authentication methods.
Adding authenticators with different factor types and method characteristics strengthens your MFA strategy. You can require authenticators for apps or groups of users and specify which ones can be used for account recovery.
|
Factor type |
Method characteristic |
Authenticator |
|---|---|---|
|
Possession |
User presence |
Email, phone, IdP |
|
User presence, Device-bound |
Custom OTP, Duo Security, Google Authenticator, Symantec VIP |
|
|
User presence, Device-bound, Hardware-protected |
YubiKey OTP |
|
|
User presence, Device-bound, Phishing-resistant |
Smart Card |
|
|
User presence, Device-bound, Phishing-resistant, Hardware-protected |
Smart Card (with Hardware option) |
|
|
Possession + Biometric |
User presence, Device-bound, Phishing-resistant, Hardware-protected |
Okta Verify, custom authenticator |
|
User presence, Device-bound, Phishing-resistant |
Passkeys (FIDO2 WebAuthn) |
|
|
Possession + Knowledge |
User presence, Device-bound, Phishing-resistant, User verifying |
Smart Card (with PIN option) |
|
User presence, Device-bound, Phishing-resistant, User verifying, Hardware-protected |
Smart Card (with PIN and Hardware options) |
|
|
Knowledge |
User presence |
Password, security question, temporary access code |
Factor types
Okta authenticators can be categorized into three factor types:
- Possession: This is something that the user has, such as a phone or an email account.
- Knowledge: This is something that the user knows, such as a password or the answer to a Security Question.
- Biometric: This is something that the user is. It represents a physical attribute of the user that a device can scan, such as the user's fingerprint or face.
Method characteristics
Factors can be categorized into several method characteristics:
- Device-bound: These authenticators are associated with a specific device.
- Hardware-protected: These authenticators require a physical device to authenticate.
- Phishing-resistant: These authenticators don't provide any authentication data that a user can share with others. Users therefore can't be tricked into sharing their credentials in phishing campaigns. See Phishing-resistant authentication and Okta solutions for phishing resistance.
- User presence: These authenticators require human interaction.
- User verifying: These authenticators prove that a specific user is the one who is authenticating.
Authenticators
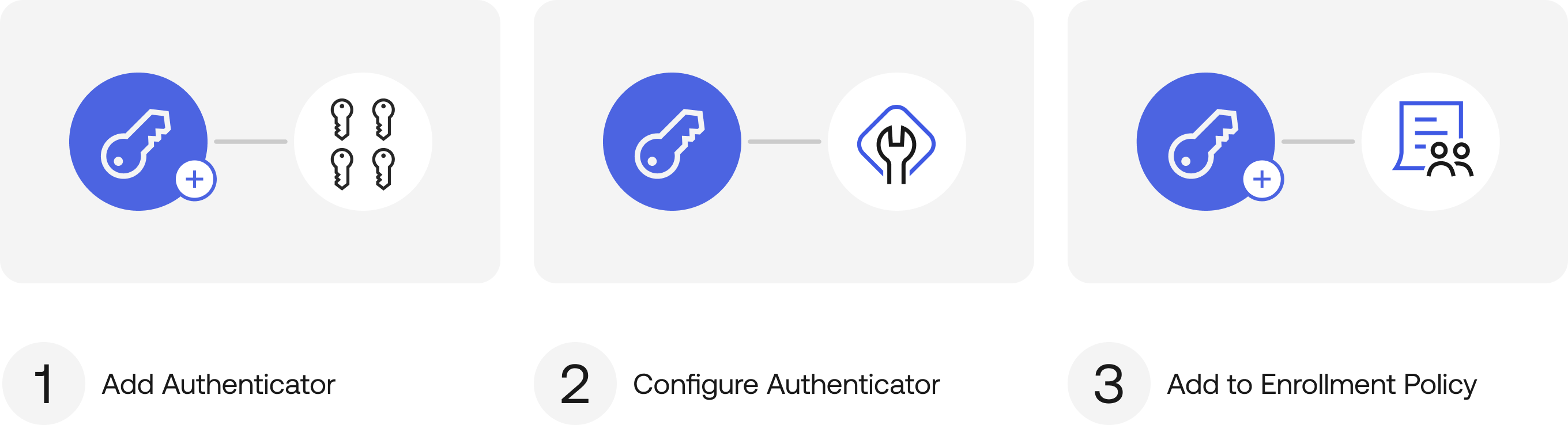
To use an authenticator, you add it from , configure it, and then add it to an enrollment policy. See any of the following authenticator topics for instructions.
- Custom authenticator
- Custom OTP
- Duo Security
- Passkeys (FIDO2 WebAuthn)
- Google Authenticator
- IdP
- Okta Verify (TOTP and Push)
- Okta FastPass
- Password
- Phone
- Security question
- Smart Card
- Symantec VIP
- Temporary access code
- YubiKey OTP
Reset authenticators
You can reset the authenticators for your users. After reset, users have to set up their authenticators again. See Reset multifactor authentication for users.