General Security
Configure various global org security settings such as user notification emails, security policies for Okta Mobile users, and Okta ThreatInsight.
To access these settings in the Admin Console, go to .
Security Notification Emails
Configure notification emails for end users by going to . If a notification email doesn't reach its recipient, an event that indicates the cause of the delivery failure (deferred, dropped, or bounced) appears in the System Log.
If your org has multiple brands, these settings apply to the default brand only. To change email recipients for a specific brand, go to . Choose the brand that you want, and then click Emails. Select a template, and then click Edit next to Audience. For more information about email notifications and template customization, see Customize an email template.
|
New sign-on notification email |
Okta sends users an email notification if they sign in from a new or unrecognized client. This email contains user sign-on details such as the web browser and operating system used to sign in, in addition to the time and location of authentication. See New sign-on notification emails for more information about the limitations for identifying new clients. Note: This feature is disabled by default for new orgs. For more information, see Sign-on notifications for end users. |
|
MFA enrolled notification email |
Okta sends users a confirmation email if they or an admin enroll in a new factor for their account. Note: This feature is enabled by default for new orgs. For more information, refer to Factor enrollment notifications for end users. |
|
MFA reset notification email |
Okta sends users an email if they or an admin reset factor for their account.
Note: This feature is enabled by default for new orgs. |
|
Password changed notification email |
Okta sends users an email notification if they change or reset the password for their account. This email contains password reset details such as the time and location of the password reset. Note:
For more information, refer to Password changed notification for end users. |
|
Report suspicious activity via email |
Suspicious Activity Reporting provides an end user with the option to report unrecognized activity from an email notification about account activity. See Suspicious Activity Reporting. |
New sign-on notification emails
New sign-on notification emails complement other security features such as multifactor authentication and shouldn't act as a replacement. In most scenarios, clients are easily and accurately identified but there are some limitations.
Notification emails for a new device sign-in are triggered when a new client is identified based on an end user's browser cookies or fingerprint.
A client can be considered new in one or more of the following scenarios:
- New browser type or version
- New operating system type or version
- New or updated app
- Unrecognized browser or operating system (appears as Unknown in the notification email)
If the authentication isn't recognized, end users should contact their admin immediately to investigate their account activity. The admin can perform actions such as terminating a user's sessions, locking the user's account, and adding multifactor authentication to improve security.
Limitations
There are some limitations that present a challenge for identification. Enabling email notifications in addition to other identifiers such as a new IP address or new location provides improved accuracy when identifying suspicious activity on an end user's account.
The current limitations for identifying new clients are as follows:
- Device fingerprints are captured after a successful sign-in.
- New device notifications may be generated when there's a change to the user's operating system or browser.
- New device notifications aren't generated for a sign-in initiated by non-Okta Identity Providers.
- The device fingerprint is based on the browser in use. The end user receives a new device notification email if they sign in with a new browser type.
- For mobile sign-ins, new device notification emails are sent based on detecting a new mobile app and not the device used to sign in.
- New device detection isn't always fully guaranteed.
- End users may receive an unexpected new or unknown device notification email if they have not signed-in to their accounts within 40 days.
For more information about end-user notifications, see Customize an email template.
Organization Security
Configure global organization settings by going to .
| IP binding for Admin Console | This setting associates admins with the IP address that they signed in from. If the IP changes during a session, the admin is signed out of Okta, and an event appears in the System Log. |
| "Remember Me" checkbox on sign in | This setting displays or hides the Remember Me checkbox for end users at the sign-in page. If an end user checks this feature and signs in, their username is remembered and displayed at sign-on until their browser cookies are cleared. |
| Activation emails are valid for | Sets the link expiry in the account activation email sent to end users. For more information about email notifications, see Customize an email template. |
| Enforce device matching for creating sessions | By default, Okta ensures that authentication redirects stay within the browser in which they were initiated. Okta compares the device identifiers provided in the requests. If they don't match, Okta denies access to the app and doesn't create an Identity Provider session. Keep this setting enabled unless Okta Support instructs you to disable it. |
| Username match criteria on sign in | This setting determines how a user profile is matched when they sign in. If you select Match entire username, users can't sign in unless they enter their full username including the domain. If you select Allow short match, users can sign in without their domain. |
| Map primary email to username | This setting changes the username to match the user's primary email address. It applies to all user types. Existing usernames aren't changed unless the primary email address changes. Select this setting if you want to enable self-service registration. |
| Users can view Recent Activity | This setting enables the Recent Activity page for users. This page displays a user's recent sign-in activity and security events for their accounts. |
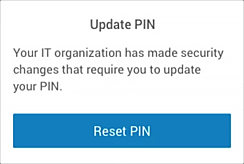
Okta Mobile Settings
Changes to Okta Mobile security settings may take up to 24 hours to be applied to all the eligible end users in your org and for Okta to prompt those end users to update their PIN.
|
PIN length |
Specify the required number of digits for the PIN. |
|
Allow simple PIN |
Select the check box to permit the use of repeating, ascending, and descending numeric sequences (such as 1111, 1234, 4321, etc.). |
|
Ask for PIN when user is inactive for |
Specify how long users can be inactive before they are prompted to enter a PIN. Users must re-authenticate after prolonged Okta Mobile inactivity. Users who haven't used Okta Mobile for 30 days or longer, are prompted to enter their Okta credentials when they eventually open Okta Mobile. This occurs because Okta Mobile relies on an internal token for authentication that expires after 30 days of inactivity. This token expiration is different than PIN and MFA expiration occurrences. |
|
PIN expires after |
Specify how long the PIN is valid before it expires. |
|
Device trust |
Select the check box to apply existing device trust app sign-in policies to apps that end users access through Okta Mobile. This setting is enabled by default. If you haven't configured device trust policies to apps, or if device trust is not enabled for your org (), selecting this setting has no effect. |
|
Screen preview/capture (Android only) |
When this option is selected, Android device users can't take screenshots, record videos, or share their screen from within Okta Mobile. Other apps are not affected. Requires Okta Mobile 3.8.0 or later versions. For iOS device users, this option has no effect. |
|
Sign on to SAML apps (iOS only) |
This iOS-specific option allows users to access SAML apps in iOS Safari by using an extension. |
Okta ThreatInsight
Okta ThreatInsight aggregates data across the Okta customer base and uses this data to detect malicious IP addresses that attempt credential-based attacks.
To prevent abuse, Okta ThreatInsight is working in a limited capacity for free trial editions. Contact Okta Support if fully functional Okta ThreatInsight is required.
See Okta ThreatInsight for more details about this feature.
Related topics