Publish Okta apps to the Workspace ONE catalog
This is an Early Access feature. To enable it, in the Okta Admin Console, go to , and then turn on Workspace1 Device Trust for your mobile platform(s).
Prerequisites
Step 2: Configure Okta application source in Workspace ONE Access
End users can continue to access apps from either the Okta dashboard or the Workspace ONE dashboard. Both experiences are fully supported. This section describes how to configure the Workspace ONE catalog to publish applications federated through Okta without the need to first import them into Workspace ONE Access. This allows admins to manage federated applications and user entitlements completely from the Okta Admin console.
If you decide to integrate Okta applications into the Workspace ONE catalog:
- Configure Okta as an application source in Workspace ONE Access (you should have done this already in STEP 2: Configure Okta application source in Workspace ONE Access ).
- Enter your Okta tenant details in the Workspace ONE Access console as described in the procedure below. You do not need to add individual applications to the Workspace ONE Access catalog.
When end users log into the Workspace ONE, the Okta apps to which they are entitled appear automatically in the catalog, along with their other apps.
Workspace ONE Access uses the Okta tenant information you configure to connect to the Okta tenant and retrieve apps and user entitlements whenever a user logs into Workspace ONE. When a user clicks an Okta app in Workspace ONE, Workspace ONE Access uses the application source configuration to launch the app.
You manage apps and user entitlements in the Okta Admin console, not in the Workspace ONE Access console. When you add or delete apps or entitlements in the Okta Admin console, the changes are replicated in end users' catalogs directly. Okta apps do not appear in the Workspace ONE Access administration console.
This integration supports the following types of Okta apps:
- SAML 2.0
- WS-Federation
- Bookmark
- OpenID Connect
Add Okta Tenant Information in Workspace ONE Access
Add your Okta tenant information and API token in the Workspace ONE Access console to enable Workspace ONE Access to connect to the Okta tenant to retrieve Okta apps and user entitlements. This is a one-time, initial configuration task.
Before you configure the tenant information in Workspace ONE Access, obtain an API token from the Okta Admin console.
Obtain an Okta API Token
Workspace ONE Access requires the Okta API token to connect with the Okta tenant and retrieve apps.
The token expires 30 days after it is last used. Each time the token is used, the expiry date is extended by
30 days.
-
In the Admin Console, click .
-
Click the Tokens tab.
-
Click Create Token.
-
Enter a name for the token.
- Click Create Token.
- Copy and save the token in a text file.
Note: After you close the window, you cannot view the token again.
Configure Okta Tenant Information in Workspace ONE Access
In the Workspace ONE Access console, enter your Okta tenant information, which is required for Workspace ONE Access to connect to the Okta tenant and retrieve apps. You need to specify the Okta Cloud URL, API token, and user search attribute.
Prerequisites
You have obtained an API token from the Okta Admin console.
Procedure
- In the Workspace ONE Access console, click the Identity & Access Management tab, then click Setup.
- Click the Okta tab.
- Enter the Okta tenant information.
Option Description Okta Cloud URL Enter your Okta tenant URL. For example, https://mytenant.example.com.Okta API Token Enter the Okta API Token you created in Obtain an API token. User Search Parameter Select the user attribute to be used to search for users in the Okta directory. You can search by userName,email, oruserPrincipalName.For example:
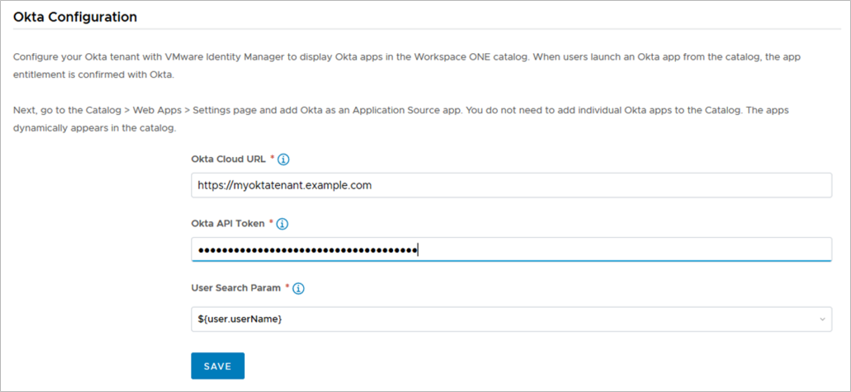
- Click Save.
Okta handles password management
Integrating Okta applications with Workspace ONE Access also automatically enables Okta password management for Workspace ONE users. No configuration is required in the Workspace ONE Access console.
In the Workspace ONE Intelligent Hub app, Workspace ONE app, and web portal, end users can change their passwords by going to Settings and clicking the Change Password link. When Okta applications are integrated with Workspace ONE Access, this password change is automatically handled by Okta, not by Workspace ONE Access.
When users change their passwords, password policies configured in the Okta Admin console are enforced. The password policy is not displayed by default on the Change Password page but appears when users enter a password that does not match the policy.